Which biometric access control system should you choose? CDVI guides you through the process and helps you find the best criteria
Advantages of Biometric Access Control Systems
High security: Biometric access control systems use unique biological characteristics, such as fingerprints, facial or retinal recognition, making them extremely difficult to copy. This greatly enhances the security of access to sensitive areas.
Reliability: Biometric characteristics are unique to each individual and do not change over time. This means that biometric systems are highly reliable and reduce the risk of unauthorised access due to forgotten passwords or lost or stolen access cards.
Ease of use: Biometric systems are very simple for everyday use. Users do not need to memorise complex passwords or carry access cards. All they need to do is provide their fingerprint, have their face scanned, or use another biometric characteristic that has already been stored.
Traceability: Biometric systems offer excellent traceability. You can easily track who has accessed a specific area at a given time, which is invaluable for the security of your building and the areas within it.
Simplified management : User management is simpler with biometric systems. Users can be added or removed easily, and specific access authorisations can be defined according to the needs of each individual.
Types of technology for access control
Access control by fingerprint recognition: This technology is based on the capture and analysis of each individual’s unique fingerprints. It is widely used because of its reliability and ease of use.
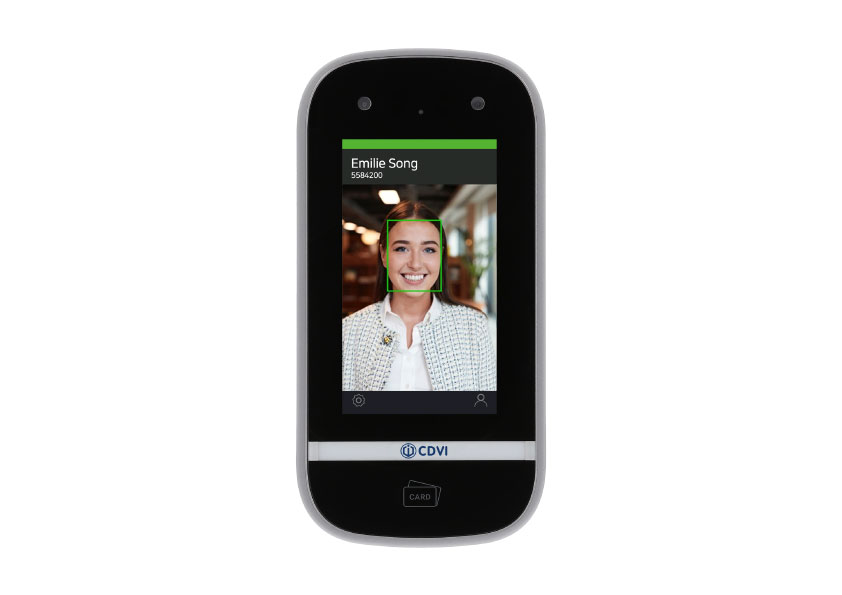
Facial recognition access control: Facial recognition identifies individuals by analysing their facial features, such as the arrangement of their eyes, nose and mouth. It is used in many applications, including smartphone security and access control. Facial recognition also has the advantage of being contactless.
Iris recognition access control: This technology analyses the unique characteristics of the eye’s iris. It offers a high degree of accuracy and security, but requires specific equipment to capture the iris, which can be costly.

9 Selection criteria for a biometric access control system
1. Level of Security Required: Determine the level of security required based on the environment in which the system will be used. Highly secure environments, such as military installations, require more robust biometric systems.
2. Reliability: Reliability is crucial. The system must deliver consistent and accurate performance, minimising authentication errors and unauthorised access.
3. Simplicity: The system should be as straightforward as possible for end users. It should not require complex training to use. Users should be able to authenticate themselves easily.
4. Speed: The speed of verification is important, particularly in environments where access must be fast. Biometric systems must be able to provide fast verification without compromising security.
5. User Management Capability: Assess the system’s ability to manage a large number of users, particularly if it is to be used in a large organisation or public space.
6. Ease of integration: The system must be easy to integrate with other existing security systems, such as video surveillance systems or traditional access control systems.
7. Resistance to forgery: Assess the system’s resistance to forgery. Biometric systems must be designed to detect and prevent forgery attempts.
8. Cost: Determine your budget and look for solutions that fit your financial resources while meeting your security needs.
9. Regulations Compliance: Ensure that the system complies with the regulations and security standards in force in your region or industry.
CDVI biometric products comply with CNIL requirements. When the user is enrolled, the fingerprint image is encrypted and transformed into a mathematical model. This model itself cannot reproduce a fingerprint image. It contains encrypted data on the timing points and flow lines of the fingerprint.
It is built from an algorithm that identifies the fingerprint with the stored template. Under no circumstances is it possible to recreate the original fingerprint image from the encrypted data.